Category: Work
Things related to work
Scientific blogging
I have seen many advices on how important it is to blog if you want to become…
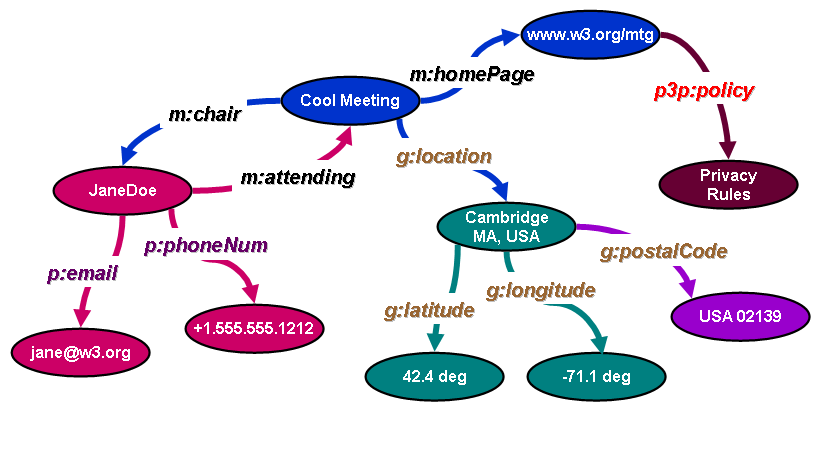
Brief introduction to Linked Data
My recent research brought me to linked data as quite interesting concept. I will here write some…
Political bot (AI) fighting human bots (using NLP and OCR)
Probably I should write this on Serbian, but to keep consistency, English it is. Since soon elections…
What is the big deal with natural language processing?
Recently here at Manchester University, at one class for all PhD students we realized that almost half…
Introducing OWASP Seraphimdroid
About 2 months ago I started thinking about creating Android security application. I was looking where the…
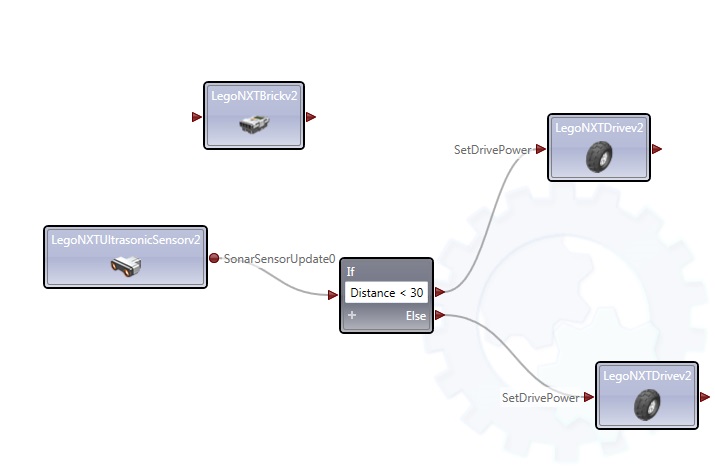
Lego Mindstorms NXT 2.0 car programmed in Microsoft Robotics
As I promissed before (https://inspiratron.org/lego-mindstorms-nxt-2-0-first-contact/), I tryed to build robot vehicle and program it using Microsoft robotics,…
Team performance – advantages of a small team
There are many teories on how to organize and how team to perform best. I would not…
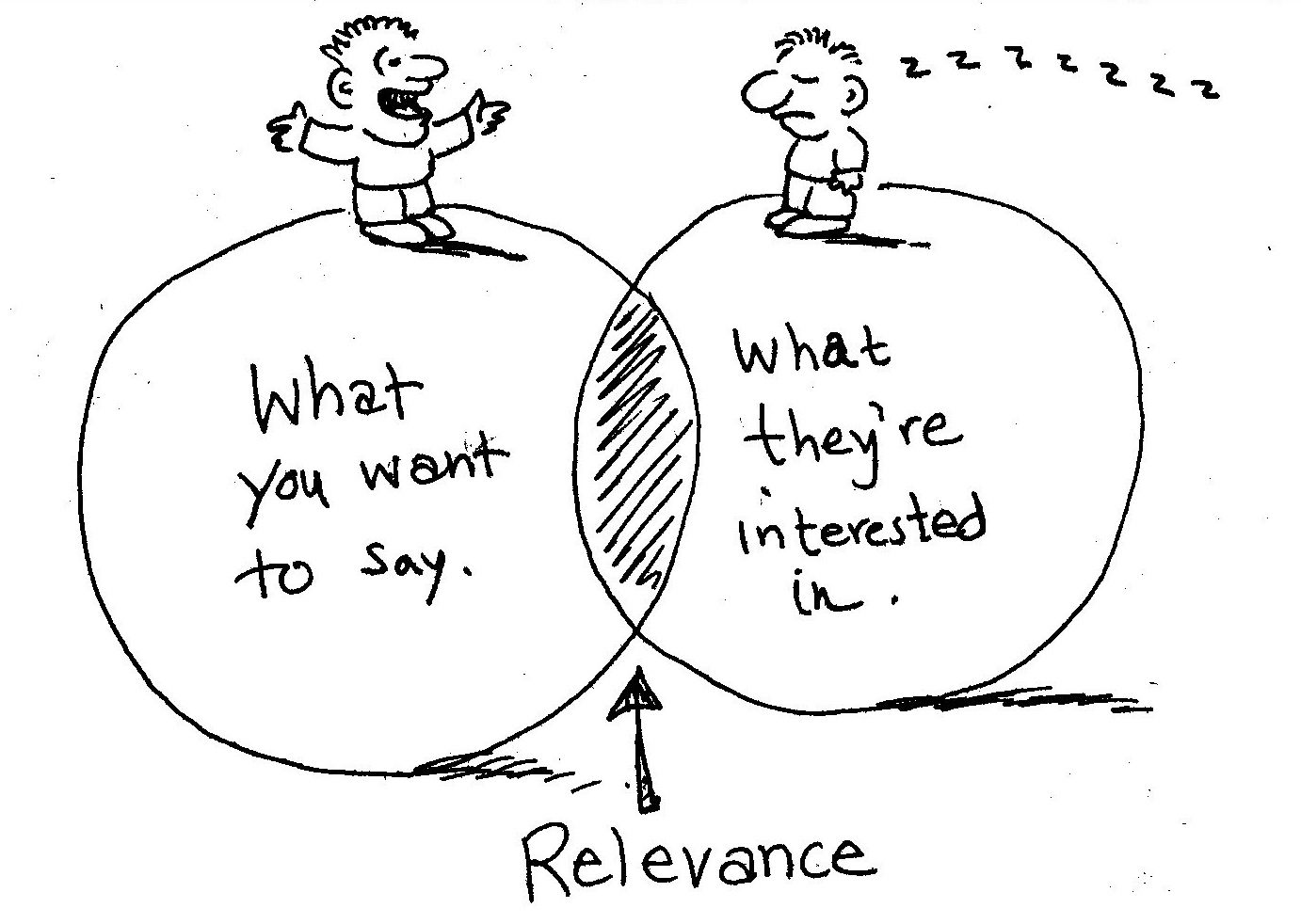
Personalized relevance classifier of sentences
In this article I would like just to pitch idea about personalized classifier, and I would like…
income.io – Money saving app
In sunday we have finaly released in Prelovac Media income.io, money saving app for Android tablets and…
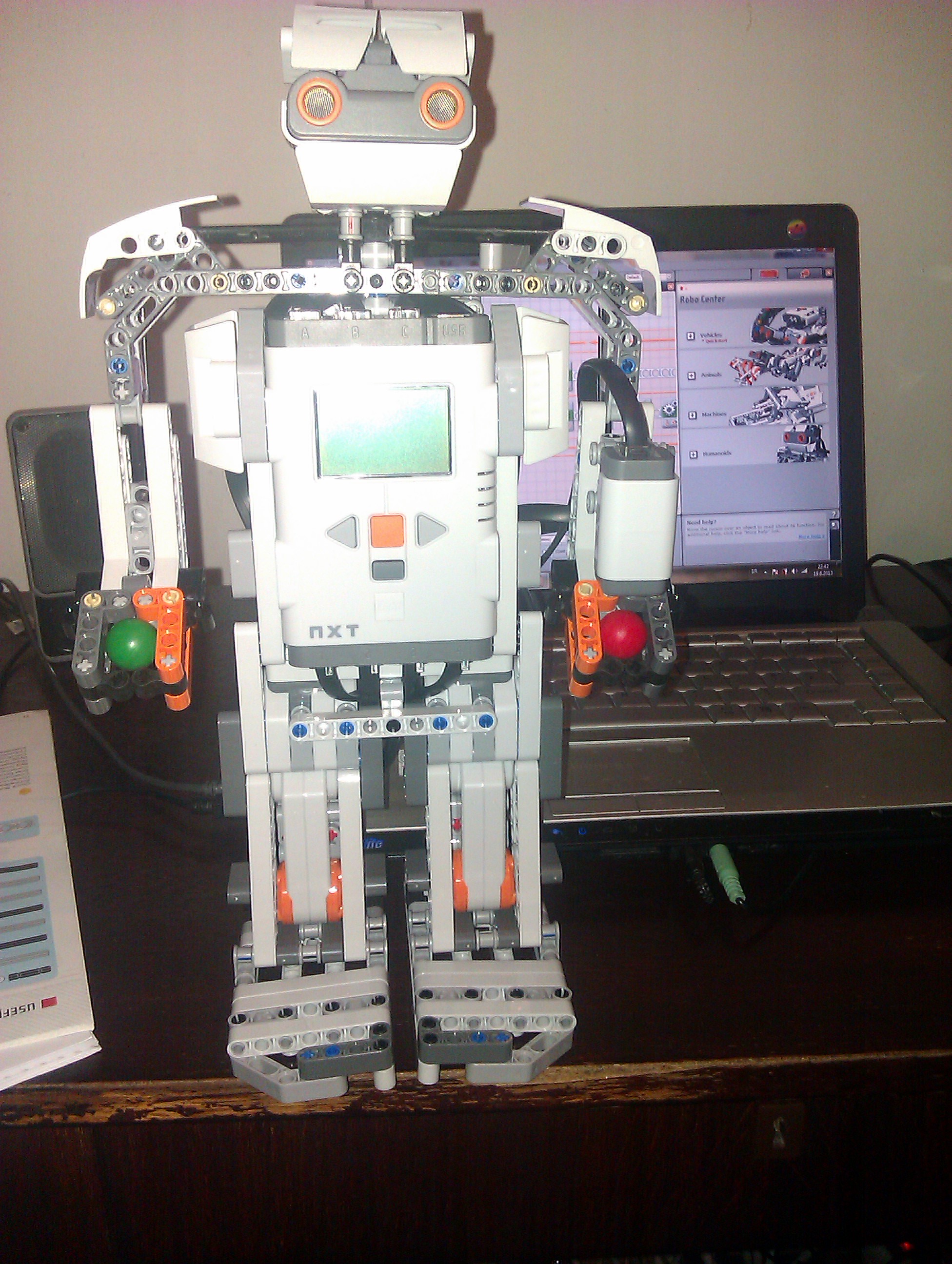
Lego Mindstorms NXT 2.0 – Humanoid first steps
I recently wrote post about my first contact with Lego Mindstorms NXT 2.0 and building robot vehicle….
Lego Mindstorms NXT 2.0 – First contact
Couple of days ago to our company arrived LEGO Mindstors NXT 2.0 robot. Today I decided to…
Introduction to Social engineering
Social engineering is one of the main security issues these days. Most of companies invest to infrastructure…