Category: InfoSec
Topics related to information security, cyber security, malware analysis, and pretty much anything related to computer security. We are quite involved in organizing OWASP chapter meetings and other security-related events. Analysis of security incidents and malware is quite a personal passion
Announcing new online courses
What is better way to share knowledge with wider audience then creating an online courses. For a…
Starting Inspiratron talks podcast
For a while, I have been preparing for this step. This blog got it’s audio podcast show…
The art of trolling and its connection to innovation
Recently I watched the following talk from DefCon named “The art of trolling”, which reminded me of…
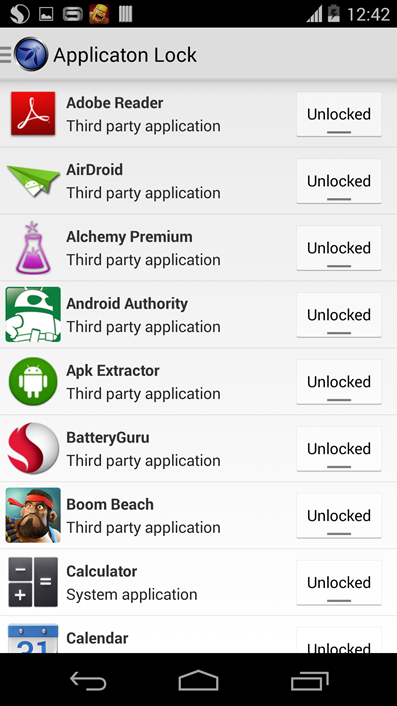
Educational framework added to OWASP Seraphimdroid
OWASP Seraphimdroid is back after Google Summer of Code with a new version, this time, it will…
Introduction to reverse engineering
1. Introduction Reverse engineering is the process of discovering the technological principles of a device, object, or…
New version of OWASP Seraphimdroid (v2.0) is published
Dear users and security aware people, we have a great announcement. The new version of OWASP Seraphimdroid…
The art of cyber war
This is the post about a lecture. Very interesting one, held on New York information security meetup…
Chasing script-kiddies and hackers on my blog
This morning, I was wondering over my admin dashboard and realized there are couple of guys (hackers…
USSD Code List for Android Smartphone
Unstructured Supplementary Service Data (USSD) is a protocol used by GSM cellular telephones to communicate with the…
Hacker’s lament
But did you, in your three-piece psychology and 1950’s technobrain ever take a look behind the eyes…
OWASP Seraphimdroid android security published
Follow my blog with Bloglovin Today I have to make one very important announcement. The first version…
Case of the cyber war: Kosovo conflict
Introduction Kosovo conflict was a conflict that started during the 1998 between FR Yugoslavia police and military…